Feature #256
openFeature #235: [Security Audit Round 2 ]
[Security Audit Round 2 ] Improper Session Management / Session Expiration too longer (Repeated)
0%
Description
Improper Session Management / Session Expiration too longer (Repeated)
observation : Repeated
CWE : CWE-613
Description :
In this application a single fixed token is in use for single user, token expiry time also
too longer.
Affected Path(s) :
https://earogya.satragroup.in/login *-Applicable to entire application
Impact :
It helps the attackers to submit without any authentication.
Evidence/Proof Of Concept :
Step 1: Login to the application with any user.And Capture the request.Here application
using the JWT token for user token as shown as below screenshot.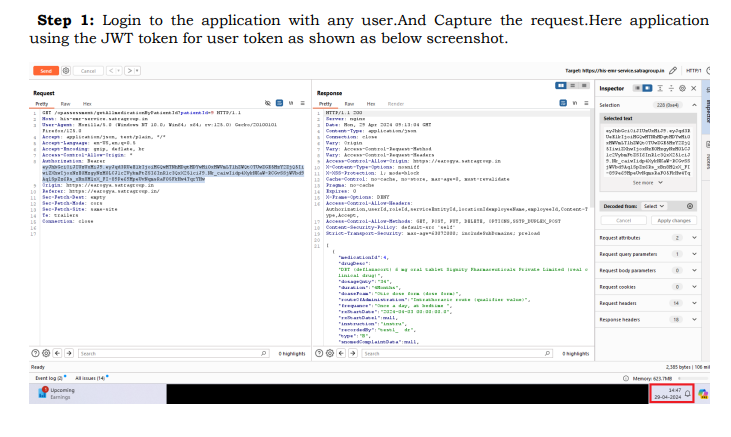
Step 2: Now, observe the expiration token of the JWT token. It is noticed that expiration time
of the token was too long as shown in below screenshot.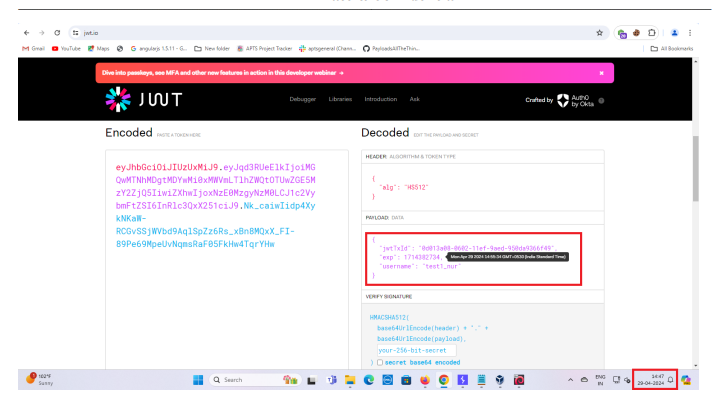
Recommendation :
It is recommended to maintain session id after login and destroy it after logout.
Reference Link: https://cheatsheetseries.owasp.org/cheatsheets/Session_Management_
Cheat_Sheet.htm
Files